Matching the increase in cutting-edge digital technologies across manufacturing have been an uptick in cyber attacks. In 2022, the average price of an industrial data breach was nearly $4.5 million. Thus, manufacturers have to remain vigilant and adopt proactive stances on cybersecurity to shield their assets, sustain operations, and safeguard their reputations.
The contemporary manufacturing sector leans heavily upon interwoven supply chains. While these networks underpin streamlined production and efficient distribution, they introduce vulnerabilities that warrant meticulous attention. While the sheer number of attack points is certainly a cause for concern, supply chains are vulnerable due to the lack of interconnectedness between individual points, as well. Unfortunately, each participant maintains its own IT architecture and cybersecurity measures, creating a complex network of potential entry points for cybercriminals.
Regulatory Compliance
Adhering to PCI DSS compliance assumes paramount importance in any supply chain. Payments occur between distributors and manufacturers almost on a weekly basis, making any payments-related vulnerabilities catastrophic, with possible results including data breaches, IP theft, and the cessation of production. To fully fathom the gravity of cybersecurity perils it becomes imperative to scrutinize authentic case studies that vividly illustrate the devastating repercussions of these attacks.
- The NotPetya Attack on Maersk. In June 2017, the global shipping colossus Maersk fell victim to the insidious NotPetya ransomware offensive. Initially targeting Ukrainian entities, NotPetya swiftly transcended national boundaries. The attack encrypted vital data and reigned havoc upon IT systems, creating operational downtime. Maersk quantified the financial result at over $300 million, and the incident showcased the fragility of interconnected global supply chains.
- Samsung. In 2022, the globally renowned technology giantfound itself in the crosshairs of a sophisticated cyberattack that sent shockwaves throughout its operations. This cyber intrusion had far-reaching consequences, disrupting Samsung's critical system and resulting in the company admitting data had been stolen. The attack led to the temporary shutdown of several manufacturing facilities and affected the company's supply chain, yet again echoing concerns about the susceptibility of modern tech conglomerates to malicious actors.
These cases highlight the incalculable consequences of cyberattacks in manufacturing and stress the importance of safeguarding the global supply chain. It is imperative to protect your enterprise and remain vigilant across the entirety of the supply chain.
Software Solutions and Challenges
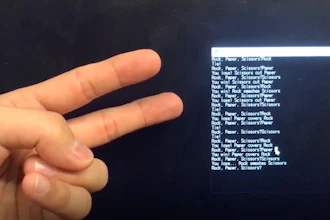
While off-the-shelf software solutions have been instrumental in optimizing manufacturing operations, they can present vulnerabilities that cyber criminals often exploit. Many common enterprise-level programs, often known as off-the-shelf software, are low-hanging fruit to hackers. Nefarious actors can devote considerable time and energy, ferreting out chinks in these universal software systems, as they sift through GitHub repositories looking for a vulnerability.
While relying on off-the-shelf software is indubitably a risk, going fully bespoke can be a mistake, as well. In such cases, manufacturers often rely on too many different platforms, which results in hackers being able to choose which surface to focus on. Instead, an enterprise should only use what it considers essential.
Manufacturing landscapes often consolidate aging legacy systems with modern technology infrastructures. The forced integration of these legacy solutions often creates compatibility issues, requiring custom patches and solutions, leaving increased opportunities for malicious actors. In our modern digital landscape, where cyber threats haunt manufacturers, proactive cybersecurity measures emerge.
The top three strategies manufacturing enterprises can immediately adopt to be proactive and fortify their protocols, identify assets, potential vulnerabilities, and the prospective impact of cyber threats include:
- Employee First Training. Invest in cybersecurity training across the organizational hierarchy, as social engineering spares no one, from the janitor all the way to the CEO. Manufacturers must provide educational content to help the workforce discern phishing ploys, social engineering scams, and other common attack vectors. Implementing rigorous access controls to limit access to sensitive data and systems is paramount, too, but critical systems should be fortified by multi-factor authentication and exclusively accessed by authorized personnel.
- Focus on Systems. Implement a robust network architecture encompassing firewalls, intrusion detection systems, and systematic network vigilance. Maintaining a vigilant posture in promptly applying software updates and patches is essential. This will alleviate the risk of exploitation from the known vulnerabilities, which is vital when working with legacy systems.
- Customize Internal Systems. Just as cybercriminals are moving away from individual targets, they’re focusing on specific third-party tools, plugins or libraries. Since an organization has less control over this type of software, hackers will try to find vulnerabilities or even impersonate an employee. That’s why organizations that deal with sensitive information should invest in custom document editing software, bespoke plugins, and backend solutions that aren’t off-the-shelf and allow for smooth integration into internal platforms. This lets an enterprise have control over its data flows and diagnose any potential weak points.
Additionally, manufacturers need to:
- Conduct recurrent security audits and penetration tests to ferret out system vulnerabilities.
- Address identified vulnerabilities without delay.
- Conform to industry-specific regulations and standards such as PCI DSS, GDPR, or NIST cybersecurity frameworks. Compliance constitutes the basis for upholding a modicum of cybersecurity hygiene.
Cyber threats are not ephemeral activities, but tangible and sophisticated dangers that manufacturers must confront head-on. It necessitates a collaboration of transparency and risk management to maintain basic cybersecurity, along with wisely choosing one’s software throughout the supply chain. Only by taking these proactive steps can the manufacturing sector continue to build the future with unwavering confidence, with an impregnable cybersecurity moat that shields its operations and fosters innovation.